That’s it. That’s the whole blog entry.
Sunday, February 22, 2026
Pro Tech? Pro Protest? Protect Your Tech and Your Neck with Protest Pro-Tips
The myth of the anonymous Internet - and it has always been a myth - is slowly fading as the average Internet user watches their protections and rights to be ignored wholly forgotten in the mad rush for capital-building information. While forensics have been able to piece together identifying markers from online activity for decades, the cost of doing that work has gone down substantially in recent totalitarian regimes. In the United States, the fourth amendment has generally held that your privacy, digital or otherwise, cannot be invaded without judicial intervention. Just cause has turned into “just ’cause” overnight with the very public dismantling of checks and balances. Private tech companies no longer worry about rolling over for fascism causing their stock to drop. Humans are no longer their customers. Speculative bubbles are more profitable and if they never have to put the money back into the pot - rather, just hand it back and forth to one another and tip their hats like playground pantomime - they are all the more happy. So why bother saving face when you can get special treatment by playing ball with dictators? That hurdle has classically been the most difficult one to overcome when doing Internet sleuthing and it has eroded entirely.
Palantir and its precursors, along with government programs like PRISM, work their way into boards and halls of tech giants. They use kickbacks, permitting, and all sorts of bribery to make sure that the biggest-named players are all in on the grift of faux security in modern tech. But tech is less secure than it has ever been. It may prevent low-rent script kiddies from scamming your Roblox account, but everything you do on most of your devices can be laid bare in seconds if someone merely decides to look.
Again, this is not new. Logging has been fundamental to computer network interaction since its inception. Things needed for reliable communication over an infrastructure made to carry flustered Trans-Atlantic accents from Pennsylvania-65000 to Klondike-5555 were already being stored so these digital bridges could be created. Endpoints had to be known. Routes had to be known. Owing to this, there was little anonymity in computing from the start. Anonymity was added, intentionally and otherwise. Log files take up space, so anonymity is bolstered simply by not storing this information past the active session. But compression got extremely good, extremely fast. Especially for text. Logs became less and less a storage concern and more one of privacy well before AOL shipped its first disk. For a while, privacy was a top tier feature in online communication. At least, behind the scenes. People love to identify themselves. It’s almost like we are all apes made of existential dread and routine. Because we are. As the net became more ubiquitous, people started realizing the importance of privacy. Not for illicit acts, though certainly those were in the mix. But for every day activities that were becoming more common online. Communication with friends, family, doctors, colleagues. These all needed some protection from prying eyes. Encryption technologies became an arms race against bad actors trying to hijack communications to steal what information they could. At the same time, however, companies began realizing how much of the data flow they controlled and how much that data could be used to create targeting for themselves. Then, they realized people would still pay for services even if ads where part of that service. In some old newsroom storage closet, William Randolph Hearst’s portrait smiled. So began the two-faced deceit of IT security.
All of this is just a long-winded intro to say this: No corporate entity ever has your best interests in mind when making decisions. Only profit. Or reduction of loss. When paramilitary police forces decide to dox you, the ’safe, secure, encrypted’ services you use from publicly traded for-profits mean absolutely nothing. They have your data. They will give it over to the cops. It’s the most financially beneficial stance (on paper), and that’s the only stance they will ever take.
So what is there to do? Break out paper cups and semaphore flags? How can you go to a protest and keep your digital life from becoming Exhibits A-Q should a stormtrooper decide you look enough like his ex or his abusive dad or just that kid he beat up in high school so it’s your day to get zip-tied and paddy-waggoned? Not all is bleak, nor do you have to pull a Full Amish when you head down to the future kettle where the first amendment is “protected” until it’s not. You can do quite a bit to harden your personal security - which in turn makes those around you more secure. It’s work, but what isn’t these days? Work, I guess.
Leave your phone at home
This is one of those pieces of advice that often gets eye-rolled by activists and organizers. But before you dismiss it, hear me out. I’m not saying ‘don’t take a phone.’ I’m saying leave the phone you use as your primary device at home. It is very easy and very cheap to pick up a second phone for recording - one of the most important functions of a phone at any protest - and communication. You can use an anonymous pre-paid carrier phone for emergencies, an old phone you’ve wiped, or grab a cheap used unlocked phone off of any number of marketplaces. Considering the despicable desposability cycle of modern phones, you can probably find a few free ones with some calls to friends and family. A few things to keep in mind:
- Fully factory reset any phone you receive or purchase. If possible, do this offline using tools from the manufacturer.
- If an alternative, hardened OS such as GrapheneOS is available for your device, consider using that instead of stock Android or the manufacturer’s bloatware.
- Try to find a phone that uses a physical SIM card. eSIMs are convenient, but are tied to the device and usually tied to the sales records of the device. A physical SIM lets you swap to another carrier or a prepaid number with ease.
- Keep apps to the bare minimum. When possible, use app stores that do not tie to an account. F-Droid is a good option. Obtainium is very popular as well.
- DISABLE BIOMETRICS. Apart from being way less secure than they purport, biometrics can be used to illegally compel you to unlock your device. Face scans are NOT legally protected. Fingerprint scans can be obtained through force. Set up a complex PIN or password and don’t fall for the false security of biometric login.
- Don’t sync accounts, contact lists, texts, etc. Don’t use e-mail applications. Check e-mail through a private browser session. This is a pain because you have to manually enter security info every single time, but it means that there’s no forensic footprint left on your phone once the session is closed.
- If you need to stream or capture to a cloud service, add a second, anonymized account for doing so. You can always re-share from your primary account later, but there’s no reason to link your activities to verifiable identification.
- Remove data from your phone when you get home. Back it up on a secure drive and remove it from the device. Again, there’s no reason to provide a free map of your whereabouts for potential prosecutors.
- Use a VPN (with manual credentials, not apps). A VPN can help protect you from local scanners, a more and more popular tool for oppressors, as well as provide an extra layer of cover from your carrier snooping on their behalf. Generally, use a VPN from a country with sound data protection laws like the Netherlands if possible.
- Utilize wifi hotspots over cellular data when possible. Many areas have free wifi if you look for it. Combined with a VPN, getting your exact activity trail becomes much, much harder.
- Only give the phone number for the device (if applicable) to a few people you trust. An army willing to use a 5 year old to draw people out of a house will absolutely put pressure on people close to you. People can’t give up your info if they don’t know it, so keep the list as small as you can.
- Use your protest phone for protesting. Keep it on Airplane Mode or turned off. Take it off Airplane Mode AFTER arriving at the protest. Put it in Airplane Mode BEFORE you leave the protest. Cell tower pings can be used to create a very accurate map of your path to and from. Again, don’t give them anything for free.
- If you simply cannot use a dedicated phone and cannot leave your phone at home, consider paring down apps, creating a second profile with very little information and using that when you’re at gatherings, using a VPN, disabling ALL AI tools, turning off tracking metrics (such as “send us data to improve your experience while using the app!” settings), signing out of social media accounts, and following the biometric and VPN suggestions above.
Be comfortable being bored
Excepting a secured phone (if necessary), don’t bring any connected devices with you. No iPad. No Switch. No Steam Deck. No ROG Steam Deck But Worse. If you have one of those handheld retro devices from Anbernic or anything with bluetooth, wifi, or mobile data, just leave it at home. Tablets, smart watches, even many MP3 players - anything that can connect with a wireless service of some type can be scanned and identified and linked to you if found on your person after an arrest. If you’re going to a protest, you’re going to protest. Not to scroll feeds or find epic mounts. Being uncomfortable with being bored is no reason to tag yourself like a migratory whale pod.
Don’t give up your entire identity at home
In your day-to-day life, more and more of your online identity is being added to your digital fingerprint. Platforms can predict, with astounding accuracy, what your next website visit will be. They can pick you out of a haystack of haystacks of users in seconds. Every cookie you accept, every permission you grant…they’ll be watching you.
Use a VPN on your home network. You don’t need to go so far as to tunnel to another country for your day to day use, but just adding one more layer of obfuscation helps. Obscurity is not security, but it’s better than nothing. Use secure communication when available. Set your browser to always use https, in example. Switch off of known problematic messaging apps like Discord to more secure options like Signal. Don’t use AI processing on anything. In fact, turn off AI everywhere you can. If you’re using Windows, [url-”https://www.howtogeek.com/how-to-rip-out-copilot-from-windows-11/” target=”new”]uninstall and prevent CoPilot from reinstalling [/url](note - this can change on a whim and they are pushing CoPilot hard, so your best bet is to leave Windows or go back to Windows 10 and use a debloating tool). Switch your search engine to a non-AI backed search such as DuckDuck Go’s No AI service. Remove AI tools from your browser if you use Chrome or Chromium based browsers or Firefox. (Note, beginning with Firefox 148, a single kill switch will be introduced under Settings -> AI Controls -> Block AI Enhancements, but it has not rolled out globally at the time of this writing).
Don’t use social media to discuss your activities at protests. You can obviously be loud and proud about your views, but any insight into the inner workings of direct action will be use to subvert it. There is no virtue signalling in protest. There’s no reason to share intel with the enemy during an active war. Save your mementos in a safe, encrypted location. Once everyone swears they were always against all of this, which they will, feel free to make a wall of dissent. But during active operations, no need to identify locations, organization, or the faces of others for internet points.
Keep your systems secure. Self-hosting can be a great way to withdraw from the onslaught of platform rot, but it can also open you up to attacks. Automated attacks are becoming more sophisticated, or in the case of AI based attacks, more frequent to the point of overwhelming systems. Not smarter, just more waves crashing against the beach. Protect yourself by understanding edge security. Make sure your router is not compromised and is up to date on its firmware. Make sure to keep an eye on security bulletins for software you host and quickly update it if a confirmed security hole is disclosed. This is obviously for more technical folks, but anyone can learn how to lock down their home network in a couple of days worth of YouTube videos and old forum posts.
Stop using Spyware as a Service
The Superbowl ad for Ring really shook the tree in terms of the general public’s understanding of just how perverse and pervasive private spying has become. Convenience has, for at least the last two decades, come at the cost of security. We hand over our details willingly to save a few steps while logging in or to scream into our personal void and have it play back our favorite comfort songs. Ditching digital servants is a minor inconvenience that feels like oppression to so many who are now used to the ease of it all. I promise, it’s really not that hard to pick a playlist by hand. Drop digital assistants from your phone. Doubly so if they’re AI-backed. Get rid of Echos and Smart Speakers and cloud-connected doorbell cameras and app-based light managers and all that BS. You can find replacements that leave all of your data in your personal network for nearly everything. So if you really need the convenience or are in a position where you need these things for accessibility, there are options. Home Assistant is a robust, multi-protocol service which can be locked down, but still control your existing closed-source hardware, in example.
Don’t use sign-in aggregators when you can avoid it. “Sign in with Google” sure feels like a convenient wonder. But what it really is is a single point of access for anyone who is able to get your Google device from you. Like the cops or TSA (cops) or ICE (somehow even more cop cops). Instead, consider an encrypted password manager with a strong master password (not biometric!) and individual site password. Avoid saving the password manager backups on cloud storage and instead, sync them to a folder on your network or an external endpoint you control. Again, passwords are protected by the 4th amendment. Your fingerprint is not.
Stop sharing videos with tracking data. YouTube, TikTok (dear god, stop using this garbage), and many other video hosting sites have a share button that tracks you and then tracks further shares by others who are NOT you. Strip your URLs before sharing them. Use only the required query string data (example - on YouTube, shares usually include an si=(code) element. When you share, remove everything except for the required video ID. When using the fully qualified www.youtube.com, this usually means deleting everything after and including the first ampersand. When using a shortened youtu.be link, this usually means deleting everything after and including the first question mark.
Example:
https://www.youtube.com/watch?v=EOxERcvYE9g&si=XXXXXXXXXXXXXX or https://youtu.be/EOxERcvYE9g?si=XXXXXXXXXXXXXX Become https://www.youtube.com/watch?v=EOxERcvYE9g or https://youtu.be/EOxERcvYE9g respectively.
Don’t use photo filter apps, AI enhancement apps, or anything that requires personal data to produce some social token. “It’s fun, everyone’s doing it and I want to see mine!” Nobody is going to care about this shit in a week. Remember BitStrip avatars? Garbage, prepackaged flash art that was reassembled after you handed over the keys to your personal profile? Nobody actually liked anyone else’s but their own. Which means nobody actually liked them. You’d give them enough info to fake a MasterCard support call and get the most dated, ugly garbage to hang on your digital sash. Stop.
The future of capitalism and the future of humanity cannot coexist. We’re living in that tumultuous between-time, when neither side has laid full claim to the next stage of development and both sides are still under the illusion of a false pact. The average person still thinks technology is a service, not a siphon. The average CEO still thinks that there is more wealth to be pumped from a dry populace. One side will crack and separating your affairs now will do nothing but benefit you, regardless of how the whole thing shakes out. Services are built to incubate product. YOU are the product. Your data. Your eyes. Your time. They sell your own atrophied ability back to you in a neatly packaged, completely standardized, wholly unowned-by-you way. Put up as many roadblocks to them getting all of you for nothing as you can.
Some other videos and resources I’ve enjoyed (GDPR protected. Click Play Video to view):
Saturday, February 21, 2026
I hate Rogue-Likes. Hades is one of my favorite games.
❗The following overview contains SPOILERS for Hades. Reader discretion is advised.❗
Gaming is Hell. From the AI slop and asset flips that pollute low-bar eshops like (checks notes) Switch and PS5 to the ever-climbing dev cycles making 300 hour experiences that demand 100% of your time for the better part of a year. Gaming is Hell.
But sometimes it can be nirvana. In the case of Rock Band, literally.
I’ve never been a fan of -like as a game description. Shorthand can express a ton of information quickly, so it’s useful for conveying a description in an elevator. But it becomes useless as a descriptor in long form reviews or in marketing material. Metroidvania is -like’s granduncle and lost every ounce of meaning the moment it was uttered. What is a Metroidvania? Not Castlevania or Metroid. Castlevania 2 is closer to the modern ideal than the first. Metroid fits the bill, but so do dozens of games that preceded it. And today it’s diluted to the point of kind of meaning any platformer where you back track with upgraded abilities. Almost always 2D, despite Metroid stepping onto the Z axis with GameCube. What’s a Rogue-Like? Rogue certainly isn’t. The concept of dying being part of gameplay is such a minor building block to a complete game, making a genre out of it seems limiting and very, very stupid.
Cards on the table. I hate cards. But I also hate ‘Rogue-likes.’ That doesn’t mean I hate games with the mechanics associated with that shorthand. But I have yet to find a game which has made that phrase a central part of their release push that does much of anything for me. Super Mario Bros. gives you information which makes your next play go a bit further. Just because its buff is your own memory, why isn’t that a Rogue-Like? You must die to get the intel to improve your next run. See what I mean? The whole concept is meaningless due to oversaturation, wibbly-wobbly edges, and mostly, the reductive boxing-in of defining a genre around a single mechanic. I roll my eyes at the term being used in reveals. Or being spat out by denizens of camp GitGud. Or, most egregious of all, on the goddamned box text.
I bring up this annoyance because often - well more often than never, which is too many times - Hades discussions will include the incantation as a way to quickly signal those GG campers to perk up their ears, while the less coordinated, but often more story-hungry of us will tune out. Rogue-like almost had me sleeping on what turned into one of my favorite games of the past 10 years. I almost looked back and watched my love vanish from my vision into the depths of the Underworld. Liam Gallagher would have been so disappointed.
I’ve played a fair number of games carrying the stupid, connotative weight of Rogue-Like and have disliked them all in some fundamental way. At best, with a game like Rogue Legacy, it was an afternoon-waster that didn’t stain my soul, but that wasn’t about to live in my head any longer than it took to see a few level styles. At worst, it was Returnal or similar fare - games that turn progress into a burden because the fall is so far on death that you can’t enjoy the game. You’re watching every step. You’re meticulously scrubbing the entire room for health. You’re not taking any risks and trying to color inside the lines to the point it stops being a game and just becomes Operation Solitaire.
Hades is not that. What Hades is is a game deserving of more than a two word hyphenate. First and foremost, Hades is grounded in its own mythology. Which is Greek mythology by way of a very liberal license. In the best way, I must add. Hades follows Zagreus via the Gantzian theory of Zag’s - his friends call him Zag. It’s cool - lineage; being the child of Hades and Persephone. This diverges a tiny bit from his myth of being reborn after being Stretch Armstronged by some Titans having a bit of a play in the yard, but the bones remain. He desires to escape the Underworld his father has built for the souls of humanity and to join the gods on Olympus. To escape, he must traverse always-changing rooms of scaling difficulty, get random boons from gods and goddesses, and frequently give 1/3rd of a very good boy many, many pets.
The mythology of Zagreus makes him a fantastic vessel for the gameplay mechanic and oxymoron of progressive death. He doesn’t die. Progress is achieved because death is, by his own myth’s telling, just a reset. Additionally, failure does not result in so massive a setback as to feel like lost time. Death (which is what we’ll call it, but not what it is) is progress. Every run gives you a little something. Longer runs become equally rewarding to succeed or to fail. Rooms nearly always contain some helpful item you can take with you after defeat, and as you make it through more rooms, the run becomes more and more valuable upon expiration. It feels like part of the game because it is part of the game, rather than being a harsh punishment. You are also rewarded with unique dialog and grounding story segments between runs, keeping you engaged. You have multiple collectable buckets that fuel multiple progression systems. Some can be used to power up the character. Some can be used to add more boons to the labyrinthine halls of the Underworld. Some are just trinkets or tokens you can give to characters to get additional permanent modifiers for future runs. The dialog is witty, impeccably acted, and very cohesive. There is a whole game upon which the mechanic of progressive death is hung, along side other equally rewarding mechanics. And that, as some poetist once penned, made all the difference.
Beyond the progression mechanics, the game is rich in playstyle choices. A number of weapons become available very quickly and allow for varied options for defeating the wandering horrors in the catacombs of the damned. Ranged, melee, bull in a china shop…whatever your preferred method of dispatching foes, you’re not too far off from unlocking a weapon that allows you to express your desire to re-kill the dead in your own way. The game does not lock you into classes - you can swap at any time. You can play your current mood and mix things up if the wind changes. You never feel stuck in a choice for very long and that makes the experience much more personal and rewarding.
The graphics are beautiful, hand-drawn, thoughtful representations of the core story. Every character is uniquely represented by their art. Yet they are all fully cohesive with every other. The game is unapologetically horny (complimentary). Gods are sex. They are manifestations of the ego interpreting the drives of the id. Hades makes that statement well, without making it gross or skeevy. The game has an absolute lust to it without being a brown paper bag Switch title where Honeys are Popped or Gals are Gunned.
The sound and music are absolute delights. Ambrosia in every word spoken. Thundering beats in time with your attacks give the game a rhythm, intended or otherwise, that really amplifies the experience. The satisfying sound of Zagreus’ dashes, slashes, bashes, and lobs are all tied so well to the animation that even as you’re playing it, the battles seem choreographed. The acting is, as mentioned, top tier. The entire audio experience is truly wonderful and utterly deserving of their many, many award nominations and wins. It’s a soundtrack you’ll want to pick up and put into rotation immediately.
Hades is not an exception to my rule of dismissing rogue-likes. It’s proof that the label bares almost no value in describing a game that has more depth than a teaspoon. To draw the breath to say it, you’ve already given yourself enough runway to accurately depict any game you’re about to besmirch. The jargon does not serve a purpose. It actively diminishes nearly any game to which it’s applied. The fact that Hades and Returnal can both be brought up in the category is enough to disprove it’s worth. But there’s no stuffing that Barbara Eden back into the Michelob tallboy. So, despite my hatred, my message is more for those of us who feel the label is off-putting. If someone voice-vomits that phrase about a new game, wipe it off your shoes and do a little research online before discounting it. While it’s true that usually you’ll find a cheese grater with the words ‘for genital use only’ etched on the side in shaking script at the end of the painbow, sometimes you may find your next favorite game.
Tuesday, February 17, 2026
Club Penguin - Gaming on Linux
I’m going to make a bold statement.
Leaving Microsoft and Apple is fighting fascism.
See? It’s bold!
In a landscape where both companies are selling out their own employees and customers for a speculation bubble around a wrong answer machine nobody asked for, anything you can do to reduce their grip on the world desktop market is - true facts - a strategy against the regime they fund. Both companies have been openly complicit in, and have directly financially benefited from the Trump administration. Benefited in a way that robs the public chest and in a way that funnels more money from their own customer base up the chain without providing any meaningful goods or services in kind. Hell, Tim Cook got a personal gold sticker from Das Uberstench. And both companies have funneled millions of dollars into his pocket in return. Both in direct contributions, indirect ones via PACs, and by laying the groundwork for theft from the masses on a scale that would have been unimaginable, even by the most mad king, a decade ago. AI is a global grift that is going to kill us all, not because the actual product is dangerous. It is dangerous. But the real danger lies in the speculation capitalist vultures…sorry, vulture capitalists…who carve its name into the heads of the spears with which they plan on hunting us. This is a fire sale. Everyone must go. Leave your belongings. Your offerings. To the gods of industry. They have always wanted to wring all of the money out of the fabric of society and they finally have the proper snake oil to oil the snakes of a totalitarian, dementia-addled Polyp Pot. CoPilot needs you to forget how to open an e-mail so it can justify speculation on compute and DC expansion. Apple will do anything to keep you in their garden of antitrust nightmares and hardware rental disguised as ownership, up to and including literally sabotaging your devices in updates. Google wants to suck every ounce of tracking data from you and everyone who looks like you to feed you, the product, the slop their real customers pay them to feed you. There is no publicly traded company that is your friend. To them, we are all prey. On the gaming side of things, the world is not much brighter. Ignoring Xbox, something the world has been trying to do since the Xbox One, Sony and Nintendo also both wish you’d just die and will them your estate. Nintendo takes every opportunity to raise prices and blame anything but their own profit graphs. They sit on a mountain of patents like a dragon, using their brigade of willing acolytes as shields for any critique. Sony kills support for anything that doesn’t turn an instant quarterly profit with little fanfare. Concord, their much hyped copy-of-a-copy Multiplicity clone of Overwatch lasted from August 23, 2024 to October of the same year; the announcement it was being cancelled coming only 10 days after launch.
Removing ownership has deep roots in fascist ideals. The idea that every single aspect of your life is run by landlords, including your entertainment, is just a small tool in a large toolbox of implements to keep the masses docile and indentured. But all normalization is a win for people who feed on the work of the world through dumb luck or birthright. People will defend their hobbies to, in some cases literally, the death and will take up arms in the name of boots if you mention they’re on their necks. Again, this is all by design. Tribalism is the fire that lights the muskets and sunk cost is the black powder within them. Just go online and say a bad word about Elden Ring or Zelda and see how fast you get your digital teeth kicked in by die-hard dickweeds who spend more time falling on swords in real life than wielding them in fantasy ones.
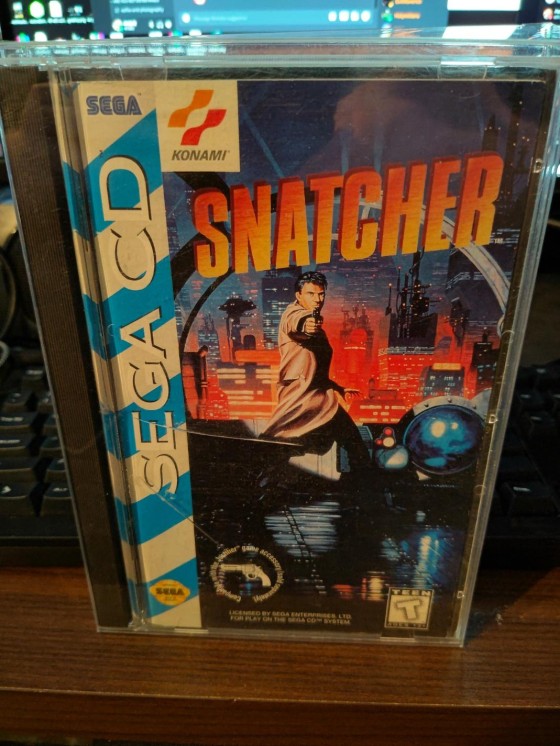
So, if you love games and hate fascism, what are you to do? Give up your hobby and become an angry person with no outlet? I mean, that’s always an option. Trust me, being a curmudgeon has its advantages. But there are alternatives. A great option, which I will surely write about in the future but that deserves its own, dedicated post, is retro gaming. There are more great games from the past you haven’t yet played than you could get to in ten lifetimes. Another is theft. And while I have zero issue with Triracy, it’s also a piece that really needs a longer deconstruction than is allowed in this post. This post is about gaming on Linux.
Linux has not had the best reputation when it comes to gaming. It has powered the OS for a number of consoles, but up until the summer of 2018, Linux gaming was mostly relegated to emulation, manually ported open-source games and a handful of dedicated releases. WINE (Wine Is Not an Emulator) existed and was useful for a handful of light weight games as well as productivity software, but for the most part if you wanted to game on Linux, you had to get source code and recompile or hope that the game developer decided to do it themselves. But in August of 2018, Proton - a joint venture between Valve and CodeWeavers - was released. Without getting too far into the weeds, Proton is a compatibility layer that diverts Win32 and Win64 calls to Linux equivalents and hosts linked libraries to process anything that doesn’t have native Linux support. Windows runs on the X86_64 platform and code assembled to that instruction set can run natively, provided the functions hosted outside of the application are available to it. Proton brokers all of this in a mostly seamless way, allowing Windows-compiled code to run without overhead under Linux. Proton uses the previous work of WINE to host DirectX, Vulkan, Open-GL, and other game-critical libraries. What this means is, nearly every game which doesn’t require kernel-level anti-cheat can be run on Linux at roughly the same (or sometimes greater) framerates as on Windows. The project is opensource, so you don’t even need Steam to run it. But Steam does work great, as well.
The Good
As mentioned, Steam is a great way to play games on Linux. Everything is mostly handled for you. You can purchase nearly every Windows-compatible game and it should run just fine on Linux with nothing but a click of the Play button. You are, of course, still beholden to Steam at this point. And to be honest, Valve is not your friend either. It’s another corporation. The only difference is, Valve has a scoped purpose and seems to be less driven to take all of your money. Just most of it.
You can, however, use their launcher without buying anything and run games through it downloaded from other sources. Itch.io, GoG (now under less evil management), or even - GASP! - CD-ROM! Additionally, there are a number of very nice, very curated launchers out there. Heroic, Lutris, Hydra, Cartriges…the list is long and full of terrors. A decent rundown can be found here. Heroic is my launcher of choice. It provides hosting for stores such as GoG and Epic, allowing you to directly install your games from the stores without downloading offline installers. The larger launchers also generally include database scraping for cover art, descriptions, and settings, allowing a curated list of games without having to manually launch each one, providing a more console-like experience.
Performance can go either way, but in general, my experience has been better framerates - likely owing to more overhead and fewer spyware processes running.
The Bad
Not all games run as easily as ‘just click Play.’ A number of GoG games, in example, require manually adding symbolic links to older libraries for audio. Some games don’t correctly implement their resolution and you end up with incorrectly scaled, hard to read experiences until you can find the right settings. The Desktop Environment you use (or don’t use) can also have a massive impact on your ability to launch games at the correct resolution the first time. Gnome, in example, generally creates a secondary desktop space and includes this in the desktop canvas sizing response to software. So many games on Gnome will show the native resolution as doubled over the actual native resolution. Window managers and compositors such as Hyprland (possibly made by a neo nazi) have less overhead and provide a better dedicated game experience, but sacrifice usability and desktop functionality for Swordfish-style tiling windows.
Configuration can be a pain with older games, as well. Games that utilize 32bit PhysX calls, in example, require extra install steps and configurations to get the full benefit of a card which supports them. Driver support is hit or miss, with native drivers generally offering the most performance, but less support from the manufacturers than the community gives the open source drivers. Nvidia can be trickier than AMD simply because Valve (again, the very sung hero of Linux gaming) uses AMD in their handheld console, the Steam Deck, and therefor has much more quality control for AMD based gaming. Nvidia generally works, but some games are more fussy about it than others. Controllers can be a mixed bag as the big players are well supported, but some X-Input controllers that work a treat on Windows will have incorrect mapping or bad support on Linux.
Overall, the difficult stuff is usually a quick web search away, but you’ll do better to search old forums or Reddit as live interaction with the Linux community is pretty toxic (another post on the ‘to do’ pile). Once you start getting a feel for how it all threads together, though, you’ll be able to self-serve most issues when they do crop up.
The Fugly
Some games just will not work on Linux. Period. This goes for some productivity software as well. Adobe, being a huge culprit of the latter. This is a sacrifice, or a dual boot setup, you’ll have to make to get out from under Microsoft for gaming. Games from Riot, in example, use Valorant anti-cheat software. This is kernel-mode anti-cheat, akin to a root kit. Frankly, for me, this is a dealbreaker anyway. I don’t want kernel mode code that is not part of the OS doing kernel mode shit. But this does cut out some heavy hitters like League of Legends. And unfortunately, there are no options unless Riot games decides to release a Linux-specific build of these games. I wanted to play Project L (presently 2KXO, which is a stupid name for stupid reasons), but am unable to thanks to this incredibly invasive anti-cheat. I didn’t even want to play it multiplayer apart from couch matches, but it doesn’t matter if you plan on going online or not. The whole enchirito is off the table.
Conclusion
Since moving to Linux, I’ve actually been gaming quite a bit more. The reason is mostly because I’m thinking about it. On Windows, gaming is a given. But when moving to a new OS, it’s often on the forefront of thought to entertain the possibilities afforded you in the journey. It’s not all rainbows and kittens and that one rainbow kitten that might grant wishes, but you can never catch it. But it can be worth the trip just to know your hobby isn’t supporting IDF bombing of children, growing the power of a little dick’dtraitor, or giving your money to a company that Thinks Different by literally making 2026 like 1984 after swearing that’s the ONE thing they wouldn’t do. Your mileage will absolutely vary, as Linux is not a monolithic operating system. But switching does make the…WINE… a bit sweeter, none the less.
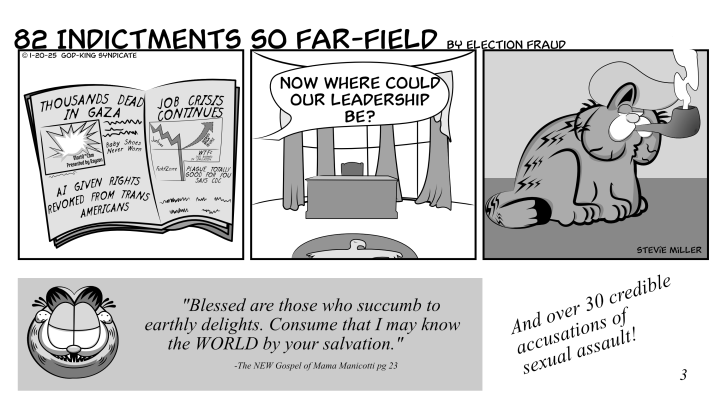
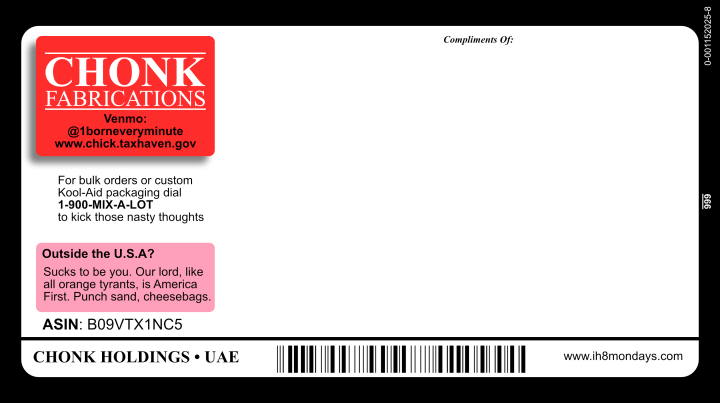
Chick Magnate
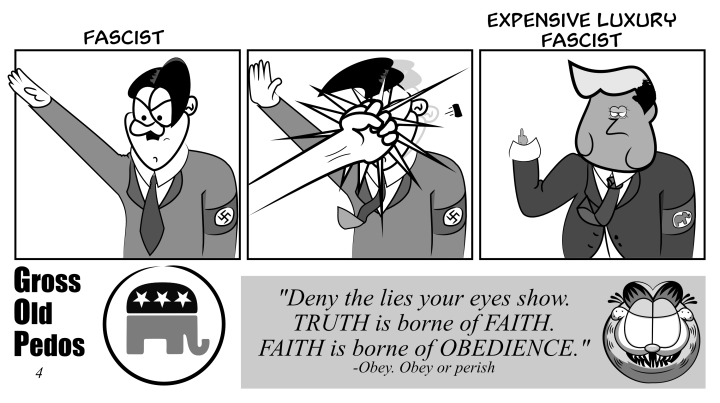
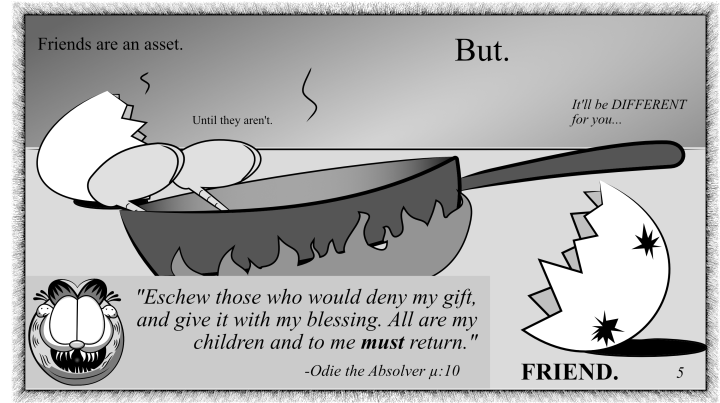
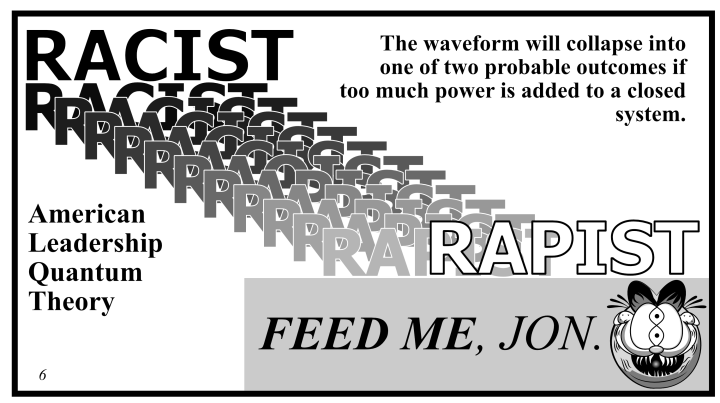
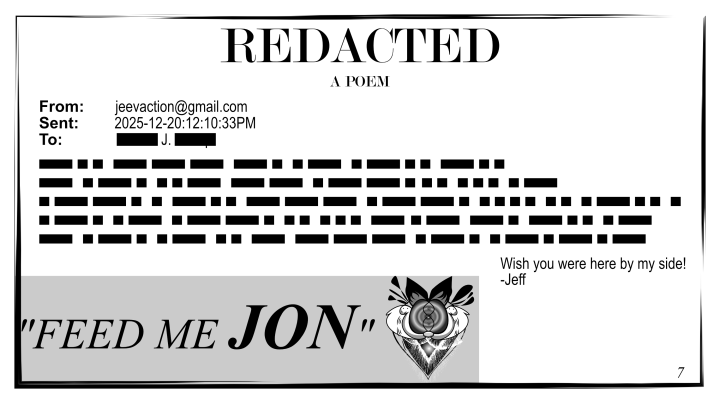
Download a print-ready copy here: CHONK TRACT 001
Note: The following images do not include descriptive alt text. Please use the PDF link above for screen readers.